Listen to the article
Key takeaways
-
Buterin sees a nontrivial 20% chance that quantum computers could break current cryptography before 2030, and he argues that Ethereum should begin preparing for that possibility.
-
A key risk involves ECDSA. Once a public key is visible onchain, a future quantum computer could, in theory, use it to recover the corresponding private key.
-
Buterin’s quantum emergency plan involves rolling back blocks, freezing EOAs and moving funds into quantum-resistant smart contract wallets.
-
Mitigation means smart contract wallets, NIST-approved post-quantum signatures and crypto-agile infrastructure that can swap schemes without chaos.
In late 2025, Ethereum co-founder Vitalik Buterin did something unusual. He put numbers on a risk that is usually discussed in sci-fi terms.
Citing forecasting platform Metaculus, Buterin said there is “about a 20% chance” that quantum computers capable of breaking today’s cryptography could arrive before 2030, with the median forecast closer to 2040.
A few months later at Devconnect in Buenos Aires, he warned that elliptic curve cryptography, the backbone of Ethereum and Bitcoin, “could break before the next US presidential election in 2028.” He also urged Ethereum to move onto quantum-resistant foundations within roughly four years.
According to him, there is a nontrivial chance of a cryptographically relevant quantum computer arriving in the 2020s; if so, then the risk belongs on Ethereum’s research roadmap. It should not be treated as something for a distant future bucket.
Did you know? As of 2025, Etherscan data shows more than 350 million unique Ethereum addresses, highlighting how widely the network has grown even though only a small share of those addresses hold meaningful balances or remain active.
Why quantum computing is a problem for Ethereum’s cryptography
Most of Ethereum’s security rests on the elliptic curve discrete logarithm (ECDLP) equation, which is the basis for the elliptic curve digital signature algorithm (ECDSA). Ethereum uses the secp256k1 elliptic curve for these signatures. Simply:
-
Your private key is a large random number.
-
Your public key is a point on the curve derived from that private key.
-
Your address is a hash of that public key.
On classical hardware, going from private key to public key is easy, but going backwards is believed to be computationally infeasible. That asymmetry is why a 256-bit key is treated as effectively unguessable.
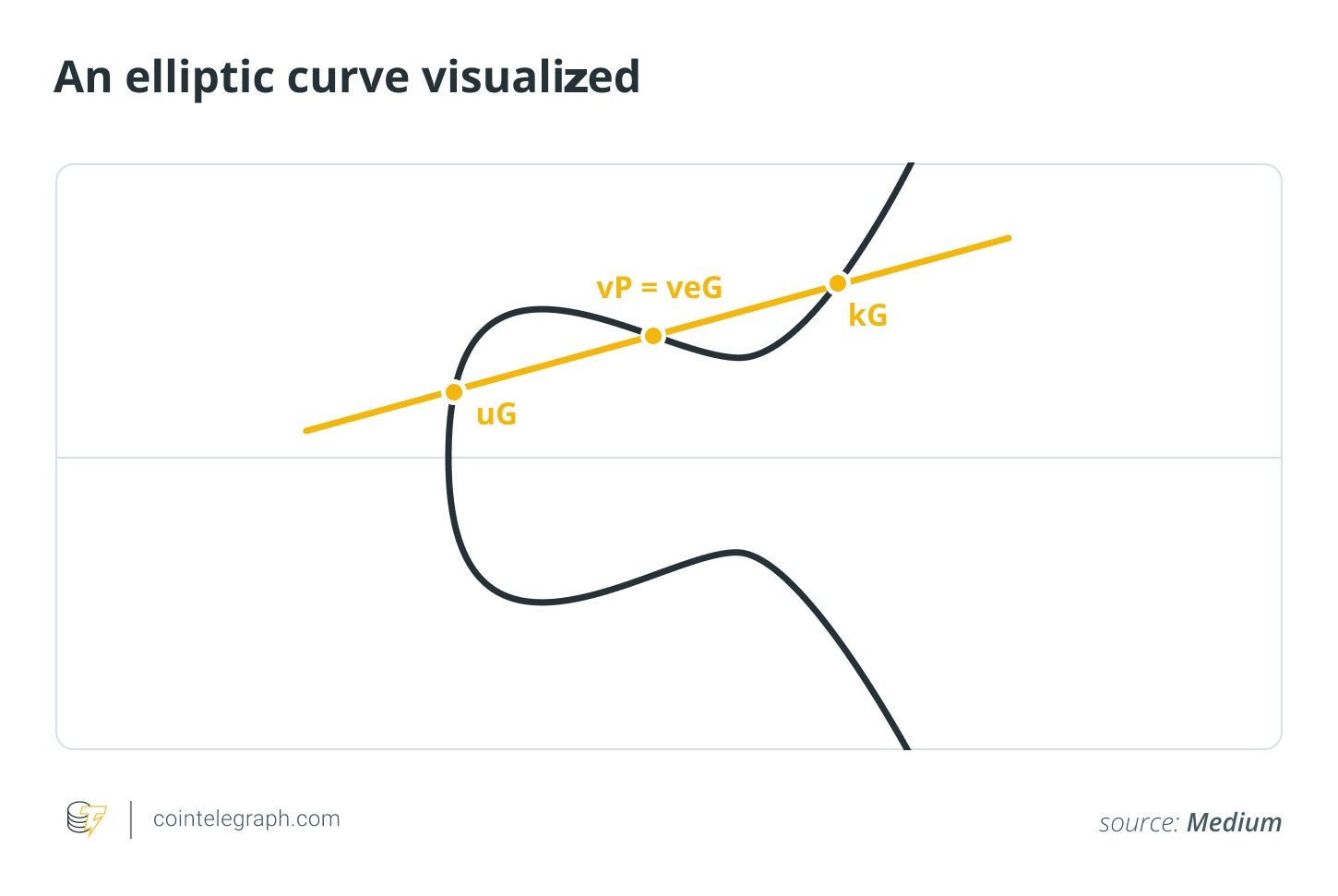
Quantum computing threatens that asymmetry. Shor’s algorithm, proposed in 1994, shows that a sufficiently powerful quantum computer could solve the discrete log equation and related factorization equations in polynomial time, which would undermine schemes like Rivest-Shamir-Adleman (RSA), Diffie-Hellman and ECDSA.
The Internet Engineering Task Force and the National Institute of Standards and Technology (NIST) both recognize that classical elliptic curve systems would be vulnerable in the presence of a cryptographically relevant quantum computer (CRQC).
Buterin’s Ethereum Research post on a potential quantum emergency highlights a key subtlety for Ethereum. If you have never spent from an address, only the hash of your public key is visible onchain, and that is still believed to be quantum safe. Once you send a transaction, your public key is revealed, which gives a future quantum attacker the raw material needed to recover your private key and drain the account.
So, the core risk is not that quantum computers break Keccak or Ethereum’s data structures; it is that a future machine could target any address whose public key has ever been exposed, which covers most user wallets and many smart contract treasuries.
What Buterin said and how he frames risk
Buterin’s recent comments have two main pieces.
First is the probability estimate. Instead of guessing himself, he pointed to Metaculus’s forecasts that put the chance of quantum computers capable of breaking today’s public key cryptography at roughly one in five before 2030. The same forecasts place the median scenario around 2040. His argument is that even this kind of tail risk is high enough for Ethereum to prepare in advance.
Second is the 2028 framing. At Devconnect, he reportedly told the audience that “elliptic curves are going to die,” citing research that suggests quantum attacks on 256-bit elliptic curves might become feasible before the 2028 US presidential election. Some coverage compressed this into a headline like “Ethereum has four years,” but his message was more nuanced:
-
Current quantum computers cannot attack Ethereum or Bitcoin today.
-
Once CRQCs exist, ECDSA and related systems become structurally unsafe.
-
Migrating a global network to post-quantum schemes takes years, so waiting for obvious danger is itself risky.
In other words, he is thinking like a safety engineer. You do not evacuate a city because there is a 20% chance of a major earthquake in the next decade, but you do reinforce the bridges while you still have time.
Did you know? IBM’s latest roadmap pairs new quantum chips, Nighthawk and Loon, with a goal of demonstrating fault-tolerant quantum computing by 2029. It also recently showed that a key quantum error correction algorithm can run efficiently on conventional AMD hardware.
Inside the “quantum emergency” hard-fork plan
Long before these recent public warnings, Buterin laid out a 2024 Ethereum Research post titled “How to hard-fork to save most users’ funds in a quantum emergency.” It sketches what Ethereum could do if a sudden quantum breakthrough blindsides the ecosystem.
Imagine a public announcement about large-scale quantum computers going live and attackers already draining ECDSA-secured wallets. What then?
Detect the attack and roll back
Ethereum would revert the chain to the last block before large-scale quantum theft became clearly visible.
Disable legacy EOA transactions
Traditional externally owned accounts (EOAs) that use ECDSA would be frozen from sending funds, which would cut off further theft through exposed public keys.
Route everything through smart-contract wallets
A new transaction type would let users prove, through a zero-knowledge STARK, that they control the original seed or derivation path — e.g., a Bitcoin Improvement Proposal (BIP) 32 HD wallet preimage, for a vulnerable address.
The proof would also specify new validation code for a quantum-resistant smart contract wallet. Once verified, control of the funds moves to that contract, which can enforce post-quantum signatures from that point on.
Batch proofs for gas efficiency
Because STARK proofs are large, the design anticipates batching. Aggregators submit bundles of proofs, which lets many users move at once while keeping each user’s secret preimage private.
Crucially, this is positioned as a last resort recovery tool, not Plan A. Buterin’s argument is that much of the protocol plumbing needed for such a fork, including account abstraction, strong ZK-proof systems and standardized quantum-safe signature schemes, can and should be built.
In that sense, quantum emergency preparedness becomes a design requirement for Ethereum infrastructure, not just an interesting thought experiment.
What the experts say about timelines
If Buterin is leaning on public forecasts, what are hardware and cryptography specialists actually saying?
On the hardware side, Google’s Willow chip, unveiled in late 2024, is one of the most advanced public quantum processors so far, with 105 physical qubits and error-corrected logical qubits that can beat classical supercomputers on specific benchmarks.
Yet Google’s quantum AI director has been explicit that “the Willow chip is not capable of breaking modern cryptography.” He estimates that breaking RSA would require millions of physical qubits and is at least 10 years out.
Academic resources point in the same direction. One widely cited analysis finds that breaking 256-bit elliptic curve cryptography within an hour using surface code-protected qubits would require tens to hundreds of millions of physical qubits, which is far beyond anything available today.
On the cryptography side, the NIST and academic groups at places like the Massachusetts Institute of Technology have warned for years that once cryptographically relevant quantum computers exist, they will break essentially all widely deployed public key systems, including RSA, Diffie-Hellman, Elliptic Curve Diffie-Hellman and ECDSA, through Shor’s algorithm. This applies both retrospectively, by decrypting harvested traffic, and prospectively, by forging signatures.
That is why the NIST has spent nearly a decade running its Post Quantum Cryptography competition and, in 2024, finalized its first three PQC standards: ML-KEM for key encapsulation and ML-DSA and SLH-DSA for signatures.
There is no expert consensus on a precise “Q-Day.” Most estimates sit in a 10-to-20-year window, although some recent work entertains optimistic scenarios where fault-tolerant attacks on elliptic curves could be possible in the late 2020s under aggressive assumptions.
Policy bodies like the US White House and the NIST take the risk seriously enough to push federal systems toward PQC by the mid-2030s, which implies a nontrivial chance that cryptographically relevant quantum computers arrive within that horizon.
Seen in that light, Buterin’s “20% by 2030” and “possibly before 2028” framing is part of a broader spectrum of risk assessments, where the real message is uncertainty plus long migration lead times, not the idea that a code-breaking machine is secretly online today.
Did you know? A 2024 National Institute of Standards and Technology and White House report estimates that it will cost around $7.1 billion for US federal agencies to migrate their systems to post-quantum cryptography between 2025 and 2035, and that is just one country’s government IT stack.
What needs to change in Ethereum if quantum progress accelerates
On the protocol and wallet side, several threads are already converging:
Account abstraction and smart-contract wallets
Moving users from bare EOAs to upgradeable smart contract wallets, through ERC-4337-style account abstraction, makes it much easier to swap out signature schemes later without emergency hard forks. Some projects already demo Lamport-style or eXtended Merkle Signature Scheme (XMSS)-style quantum-resistant wallets on Ethereum today.
Post-quantum signature schemes
Ethereum will need to pick (and battle-test) one or more PQC signature families (likely from the NIST’s ML-DSA/SLH-DSA or hash-based constructions) and work through trade-offs in key size, signature size, verification cost and smart contract integration.
Crypto agility for the rest of the stack
Elliptic curves are not just used for user keys. BLS signatures, KZG commitments and some rollup proving systems also rely on discrete log hardness. A serious quantum resilient roadmap needs alternatives for those building blocks as well.
On the social and governance side, Buterin’s quantum emergency fork proposal is a reminder of how much coordination any real response would require. Even with perfect cryptography, rolling back blocks, freezing legacy accounts or enforcing a mass key migration would be politically and operationally contentious. That is part of why he and other researchers argue for:
-
Building kill switch or quantum canary mechanisms that can automatically trigger migration rules once a smaller, deliberately vulnerable test asset is provably broken.
-
Treating post-quantum migration as a gradual opt-in process that users can adopt long before any credible attack rather than a last-minute scramble.
For individuals and institutions, the near-term checklist is simpler:
-
Prefer wallets and custody setups that can upgrade their cryptography without forcing a move to entirely new addresses.
-
Avoid unnecessary address reuse so fewer public keys are exposed onchain.
-
Track Ethereum’s eventual post-quantum signature choices and be ready to migrate once robust tooling is available.
Quantum risk should be treated the way engineers think about floods or earthquakes. It is unlikely to destroy your house this year, but likely enough over a long horizon that it makes sense to design the foundations with that in mind.
Read the full article here
Fact Checker
Verify the accuracy of this article using AI-powered analysis and real-time sources.


